Beware This Google Drive Phishing Scam Is Making Another Round
- Posted by: Top Speed
We originally published this blog on our DataBits News site in early 2014, but as it appears to be making the rounds again we want to make sure everyone has been forewarned.
With sharing of documents becoming more and more common this phishing scam is trying to scam people on a platform many people are comfortable using and sharing information through on a daily basis.
Like most phishing scams this one arrives via email with the subject of “Documents” "Invoice" or "Tracking Information". Naturally once you look at the body of the email it tells you to click on what looks like a Google Drive link to an important document.
This is where it gets particularly scary, if you click on this link you are taken to a login page that looks exactly like every other Google login page you’ve ever seen. This “fake page is actually hosted on Google’s servers and is served over SSL, making the page even more convincing,” Nick Johnston of Symantec wrote in his blog. Johnston continued, “The scammers have simply created a folder inside a Google Drive account, marked it as public, loaded a file there, and then used Google Drive’s preview feature to get a publicly-accessible URL to include in their messages.”
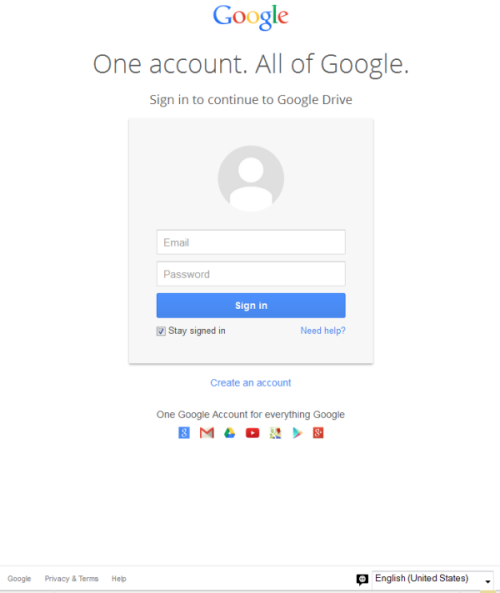
So it has a google.com URL, and it looks like a Google login. Unfortunately many people are likely to enter their login credentials without a second thought – and just like that their credentials will be compromised.
What can you do to protect yourself? First is to stay alert. If an email comes to you with the subject of “Documents” or "Invoice" but you don’t know the sender there is no reason to click that link. If an email comes to you with the subject of “Documents” or "Invoice" and you do know the sender think before opening it, would this person be sending me a document like this, even if they do send me docs do they ever just call them “documents” or "invoice"?
Second you may notice that something is slightly off with how a login is happening, for instance in this case when you click the link it asks you to sign in to a Google account. Most Google users right now could type in gmail.com or drive.google.com and it won’t ask for your credentials. Certain parts of Google, like the merchant login, always ask for you to re-enter your password, but most won’t. This is a very subtle hint that not all is right with this link, but it is one you might pick up on.
Johnston went on to say, “Google accounts are a valuable target for phishers, as they can be used to access many services…” Not only will they now have access to your Gmail, Google Drive, and Google Merchant accounts, they will have access to what is becoming more and more important in the land of cyber crime and phishing scams – access to the contact list associated with your email address!
Why is that connection so important and valuable? It’s simple, people are getting more wary of emails with links and attachments that come from Jane Smith, but if that email is from an old college friend or a neighbor down the block, you're more likely to click on the link or attachment it contains. Compromised contact lists are becoming a hot commodity to really increase the effectiveness of phishing scams, generally referred to as spear phishing as they are now aiming for a specific person or group of people connected to the compromised account.
What can you do to make sure your account stays secure. Be careful with any link or attachment that arrives via email. Don’t feel embarrassed about contacting a sender to make sure the email you’ve received is legitimate, it’s always better to ask than have your information stolen. And make sure you have taken steps to secure your password and that it’s not “password”. If that seems too obvious keep in mind in 2013 when Facebook accounts were hacked the most common password exposed was “password”.



 So nearly everyone is talking about Apple and security, but almost no one is providing the facts in the conversation. On the one side you have SECURITY, PRIVACY, GOVERNMENT OVERREACH, on the other side you have NATIONAL SECURITY and SAFETY OF ALL AMERICANS. But around the hype what are the actual facts?
So nearly everyone is talking about Apple and security, but almost no one is providing the facts in the conversation. On the one side you have SECURITY, PRIVACY, GOVERNMENT OVERREACH, on the other side you have NATIONAL SECURITY and SAFETY OF ALL AMERICANS. But around the hype what are the actual facts?


